Cybersecurity
CVE-2026-28289: FreeScout RCE via .htaccess Patch Bypass and TOCTOU Flaw
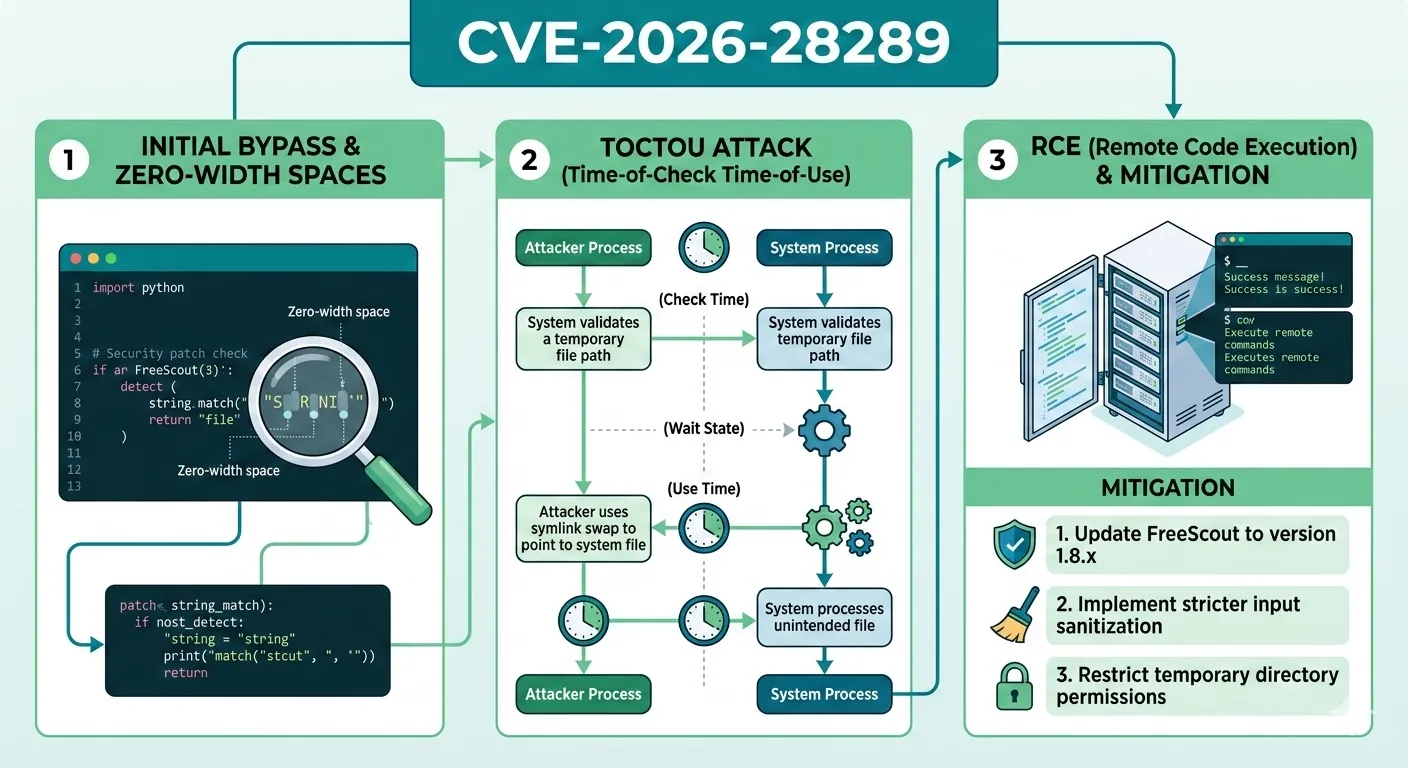
When a security patch itself becomes the attack surface, the consequences ripple far beyond the original vulnerability. CVE-2026-28289 exposes a critical patch bypass in FreeScout, the popular open-source help desk built on Laravel, where a previously fixed Remote Code Execution (RCE) vulnerability resurfaces through a clever combination of zero-width space characters and a Time-of-Check to Time-of-Use (TOCTOU) flaw. This vulnerability affects all authenticated users with file upload permissions in FreeScout 1.8.206 and earlier, turning a routine ticket attachment into a server takeover vector. Understanding how this bypass works is essential not only for FreeScout administrators but for any developer implementing file upload sanitization logic in web applications.
What Is FreeScout and Why Does This Matter
FreeScout is a self-hosted, open-source help desk and shared mailbox application built with PHP and the Laravel framework. Organizations deploy it to manage customer support tickets, shared email inboxes, and team collaboration workflows. Because FreeScout handles direct customer communication, it typically sits within the internal network perimeter of an organization with access to sensitive customer data, internal email flows, and often database credentials stored in environment files.
An RCE vulnerability in this context means an attacker who has gained any level of authenticated access, even a low-privilege support agent account, can execute arbitrary code on the server. This could lead to full server compromise, lateral movement within the network, exfiltration of customer data, and deployment of persistent backdoors. The fact that this is a patch bypass makes it especially dangerous: organizations that diligently applied the fix for CVE-2026-27636 may have assumed they were protected, creating a false sense of security.
In a real-world deployment scenario, consider a mid-sized company running FreeScout on a shared hosting environment. A compromised support agent account, obtained through credential stuffing or phishing, gives the attacker file upload permissions. With CVE-2026-28289, that single compromised account becomes the entry point for complete infrastructure compromise.
The Original Vulnerability: CVE-2026-27636
To understand the bypass, we first need to examine what CVE-2026-27636 addressed. The original vulnerability allowed authenticated users to upload malicious .htaccess files through the file attachment functionality in FreeScout. Apache web servers interpret .htaccess files as per-directory configuration directives, which means uploading one to an accessible directory can override server behavior, including enabling PHP execution in directories where it should be disabled.
An attacker could craft an .htaccess file with directives like AddType application/x-httpd-php .txt, which would cause the server to execute any uploaded .txt file as PHP code. Combined with a separately uploaded text file containing PHP payloads, this achieves Remote Code Execution.
The patch for CVE-2026-27636 added a check in the sanitizeUploadedFileName() function within app/Http/Helper.php to detect and block filenames beginning with a dot character. The intent was straightforward: since .htaccess starts with a dot, rejecting all dot-prefixed filenames should prevent the attack. However, this fix contained a subtle but critical flaw in its execution order.
This pattern of applying a narrowly scoped patch without considering the broader input space is one of the most frequent causes of security regressions. A robust patch should account not just for the specific exploit demonstrated, but for the entire class of attacks it represents.
CVE-2026-28289: Anatomy of the Patch Bypass
Zero-Width Space Characters as an Evasion Technique
Unicode includes several characters that have zero visual width when rendered. The most common is the Zero-Width Space (U+200B), but others include the Zero-Width Non-Joiner (U+200C), Zero-Width Joiner (U+200D), and the Word Joiner (U+2060). These characters are legitimate parts of the Unicode standard, used for controlling text rendering in languages like Arabic and Thai. However, they become powerful evasion tools when security logic operates on raw byte sequences without proper Unicode normalization.
In the context of CVE-2026-28289, an attacker prepends a zero-width space character (U+200B) to the filename, creating a string like \u200B.htaccess. To the eye, this filename appears identical to .htaccess. To a byte-level comparison checking if the first character is a dot, the first character is actually the zero-width space, meaning the dot-prefix check passes because the filename does not technically start with a dot.
This class of Unicode-based evasion extends far beyond file uploads. Homoglyph attacks on domain names, bidirectional override characters in source code repositories, and invisible character injection in form fields all exploit the same fundamental gap between human perception and programmatic byte processing. Developers who only test with ASCII inputs will consistently miss these attack vectors.
The TOCTOU Flaw in sanitizeUploadedFileName()
The critical architectural flaw is a Time-of-Check to Time-of-Use (TOCTOU) race condition in the logic of the function. The sanitizeUploadedFileName() function performs its security checks in the following order:
- Check: Verify the filename does not start with a dot character
- Sanitize: Remove invisible characters (including zero-width spaces) from the filename
- Use: Save the file with the sanitized filename
The problem is that step 1 (the security check) runs before step 2 (the sanitization). When the attacker submits \u200B.htaccess, the check in step 1 sees a filename starting with a zero-width space, not a dot, so it passes validation. Then step 2 strips the invisible character, producing the clean filename .htaccess. Finally, step 3 saves the file as .htaccess, exactly what the original vulnerability (CVE-2026-27636) was supposed to prevent.
This is a textbook TOCTOU vulnerability: the state of the data at the time of checking (contains invisible prefix) differs from the state at the time of use (invisible prefix removed), and the security decision was made based on the stale state.
Understanding the Fix in Version 1.8.207
The correct approach, implemented in FreeScout 1.8.207, reverses the operation order: sanitize first, then check. By stripping all invisible and control characters from the filename before performing any security validation, the function ensures that the security check operates on the actual filename that will be written to disk. This eliminates the TOCTOU gap entirely.
This fix reflects a fundamental principle in secure input processing: canonicalize before you validate. Any transformation applied after validation creates a window where the validated state may no longer reflect the actual data being processed.
Technical Deep Dive: The Vulnerable Code Path
The vulnerability resides in app/Http/Helper.php within the sanitizeUploadedFileName() function. Here is a simplified representation of the vulnerable logic:
public static function sanitizeUploadedFileName($filename)
{
// SECURITY CHECK (Step 1) - runs on unsanitized input
if (strpos($filename, '.') === 0) {
$filename = 'file_' . $filename;
}
// SANITIZATION (Step 2) - removes invisible characters AFTER the check
$filename = preg_replace(
'/[\x00-\x1F\x7F\x{200B}-\x{200D}\x{FEFF}]/u',
'',
$filename
);
return $filename;
}The strpos($filename, '.') check tests whether the first byte of the filename is a dot. When the filename is \u200B.htaccess, the first bytes are the UTF-8 encoding of U+200B (which is 0xE2 0x80 0x8B), not a dot (0x2E). The check passes, and the subsequent regex strips the zero-width space, leaving .htaccess as the final filename.
A critical nuance here is that the strpos() function in PHP operates at the byte level, not the character level. This means it will always compare the raw first byte against the dot character. Even multibyte-aware alternatives like mb_strpos() would not help here because the zero-width space is a valid distinct character that genuinely precedes the dot in the string.
The corrected version moves the regex sanitization before the dot check, ensuring that any invisible characters are stripped before the security validation takes place. This simple reordering of two lines of code eliminates the vulnerability entirely.
Real-World Attack Scenario: Shared Hosting Compromise
Consider an organization running FreeScout on Apache with a shared hosting provider. The attack scenario unfolds as follows:
- The attacker obtains credentials for a low-privilege support agent account through credential stuffing against a leaked database
- Using the support interface, the attacker creates a new ticket and attaches a file named
\u200B.htaccesscontaining the directiveAddType application/x-httpd-php .jpg - The
sanitizeUploadedFileName()function in FreeScout checks the filename, sees it does not start with a dot, and allows the upload - The sanitization step strips the zero-width space, saving the file as
.htaccessin the uploads directory - The attacker then uploads a second attachment: a file named
avatar.jpgcontaining PHP code such as<?php system($_GET['cmd']); ?> - Apache processes the
.htaccessdirective, now treating.jpgfiles as PHP scripts in that directory - The attacker requests
/storage/uploads/avatar.jpg?cmd=whoamiand achieves code execution
On a shared hosting environment, this server compromise can cascade. The attacker can read environment files containing database credentials, access files belonging to other tenants on the same server, install cryptocurrency miners, or establish reverse shells for persistent access. The blast radius extends well beyond the FreeScout application itself.
Impact Assessment and Scalability Concerns
The scalability impact of this vulnerability depends on the deployment architecture. Single-server deployments face complete compromise through a single exploitation. In containerized environments, the blast radius may be limited to the container, though container escape techniques could extend the attack. Load-balanced deployments present an interesting case: the malicious .htaccess file only lands on one server, meaning the attacker must either target requests to that specific backend or upload the file multiple times to ensure coverage across all instances.
From a detection standpoint, the zero-width space character makes this attack particularly difficult to identify through traditional log analysis. The filename appears as .htaccess in most log viewers, making it indistinguishable from a legitimate configuration file. Security teams need byte-level log analysis or specific IDS signatures matching the UTF-8 encoding of zero-width characters in multipart form data to detect this attack in progress.
Organizations running multiple FreeScout instances for different departments or clients face compound risk. A single compromised agent credential could cascade across the entire help desk infrastructure if shared authentication or SSO is in use.
Common Mistakes Developers Make with File Upload Security
CVE-2026-28289 illustrates several patterns that developers frequently get wrong when implementing file upload security:
- Validating before canonicalization: The most critical mistake in this case. Any time input undergoes transformation after validation, there is a potential bypass. Always normalize, decode, and sanitize input before applying security rules.
- Relying on filename checks alone: Filenames are entirely attacker-controlled. Robust file upload security should include content-type verification, magic byte inspection, and ideally, storing files with server-generated names rather than user-provided ones.
- Ignoring Unicode complexity: ASCII-centric security logic breaks in the face of the vast Unicode character space. Zero-width characters, direction override characters (U+202E), and homoglyph attacks all exploit the gap between what a developer sees and what the code processes.
- Storing uploads in web-accessible directories: Even with perfect filename validation, serving uploaded files directly through the web server creates risk. Files should be stored outside the web root and served through a controller that sets appropriate headers.
- Treating patches as complete fixes: The existence of CVE-2026-28289 as a bypass of CVE-2026-27636 demonstrates that patches deserve the same adversarial scrutiny as original code. Patch review should include testing with encoded, obfuscated, and edge-case inputs.
File Upload Sanitization Approaches Compared
| Approach | TOCTOU Safe | Unicode Safe | Complexity | Recommendation |
|---|---|---|---|---|
| Blacklist filename extensions | Depends on order | No | Low | Avoid |
| Whitelist filename extensions | Depends on order | No | Low | Better, but insufficient alone |
| Canonicalize then validate | Yes | Yes | Medium | Recommended |
| Server-generated filenames | Yes | Yes | Medium | Strongly recommended |
| Store outside web root + serve via controller | Yes | Yes | Medium-High | Best practice |
The most robust approach combines server-generated filenames with storage outside the web root. This eliminates the entire class of filename-based attacks regardless of the correctness of the sanitization logic. The original filename can be preserved in a database record for display purposes while the actual file on disk uses a UUID or hash-based name.
Mitigation and Remediation Strategies
For FreeScout administrators, the immediate remediation is straightforward: upgrade to version 1.8.207 or later. However, defense-in-depth strategies should also be considered:
- Review Apache configuration: Ensure
AllowOverride Noneis set for upload directories, preventing.htaccessfiles from being processed entirely. This single configuration change neutralizes this entire attack class. - Implement Web Application Firewall rules: Configure WAF rules to detect and block zero-width characters and other Unicode control characters in multipart form data filenames.
- Audit file upload directories: Check for any existing
.htaccessfiles in the upload directories of FreeScout that may indicate prior exploitation. - Switch to Nginx: If possible, migrating from Apache to Nginx eliminates
.htaccess-based attacks entirely, as Nginx does not support per-directory configuration files. - Restrict upload permissions: Apply the principle of least privilege. Not every support agent needs file upload capabilities.
For developers building file upload functionality in other applications, the key takeaway is to adopt a defense-in-depth approach. Never rely on a single sanitization function as the sole security boundary. Layer multiple controls: canonicalize inputs, validate aggressively, store files safely, and configure the web server to minimize the impact of any bypass.
Frequently Asked Questions
Does CVE-2026-28289 affect FreeScout installations running on Nginx?
The core vulnerability, the TOCTOU flaw and filename bypass, exists regardless of the web server. However, the specific exploitation path via .htaccess files only works on Apache. Nginx does not process .htaccess files, so the RCE chain cannot be completed on Nginx deployments. That said, the underlying code flaw should still be patched to prevent potential future exploitation vectors.
Can this vulnerability be exploited by unauthenticated attackers?
No. CVE-2026-28289 requires authentication and file upload permissions within FreeScout. However, because FreeScout is a help desk application, many organizations grant file upload permissions to all support agents. A compromised agent account through phishing, credential stuffing, or insider threat is sufficient to exploit this vulnerability.
What is the difference between CVE-2026-27636 and CVE-2026-28289?
CVE-2026-27636 was the original vulnerability that allowed uploading .htaccess files. It was patched by adding a dot-prefix check. CVE-2026-28289 is a bypass of that patch, using zero-width space characters to evade the dot-prefix check due to a TOCTOU flaw in the execution order of the sanitization function. Both result in the same impact: Remote Code Execution through malicious .htaccess files.
How can I check if my FreeScout instance was already compromised?
Search for any .htaccess files in the storage and upload directories of FreeScout. Examine web server access logs for requests to uploaded files with query parameters (which could indicate webshell usage). Check for any unexpected PHP files in upload directories. Review system processes for suspicious activity originating from the web server user.
Why do zero-width space characters exist if they cause security issues?
Zero-width characters serve legitimate typographic purposes. The Zero-Width Space (U+200B) indicates word boundaries in scripts without explicit spacing like Thai. The Zero-Width Joiner and Non-Joiner control ligature formation in Arabic and Indic scripts. The security issue arises not from these characters existing, but from applications failing to account for them during input validation and sanitization.
Conclusion
CVE-2026-28289 is a compelling case study in why security patches themselves need adversarial review. A well-intentioned fix that placed its validation before sanitization created a TOCTOU gap exploitable through the zero-width characters available in Unicode. For FreeScout users, upgrading to 1.8.207 is critical. For the broader development community, this vulnerability reinforces a fundamental security principle: always canonicalize input before validation. The order of operations in security-critical code is not a detail; it is the architecture. Review your own file upload handling, check the order of your sanitization steps, and consider whether your security checks would survive an attacker who understands Unicode better than your code does.
Share this post
Subscribe
Get the latest posts delivered right to your inbox.



Leave a comment