Cybersecurity
CVE-2019-25475: Buffer Overflow in SQL Server Password Changer 1.90
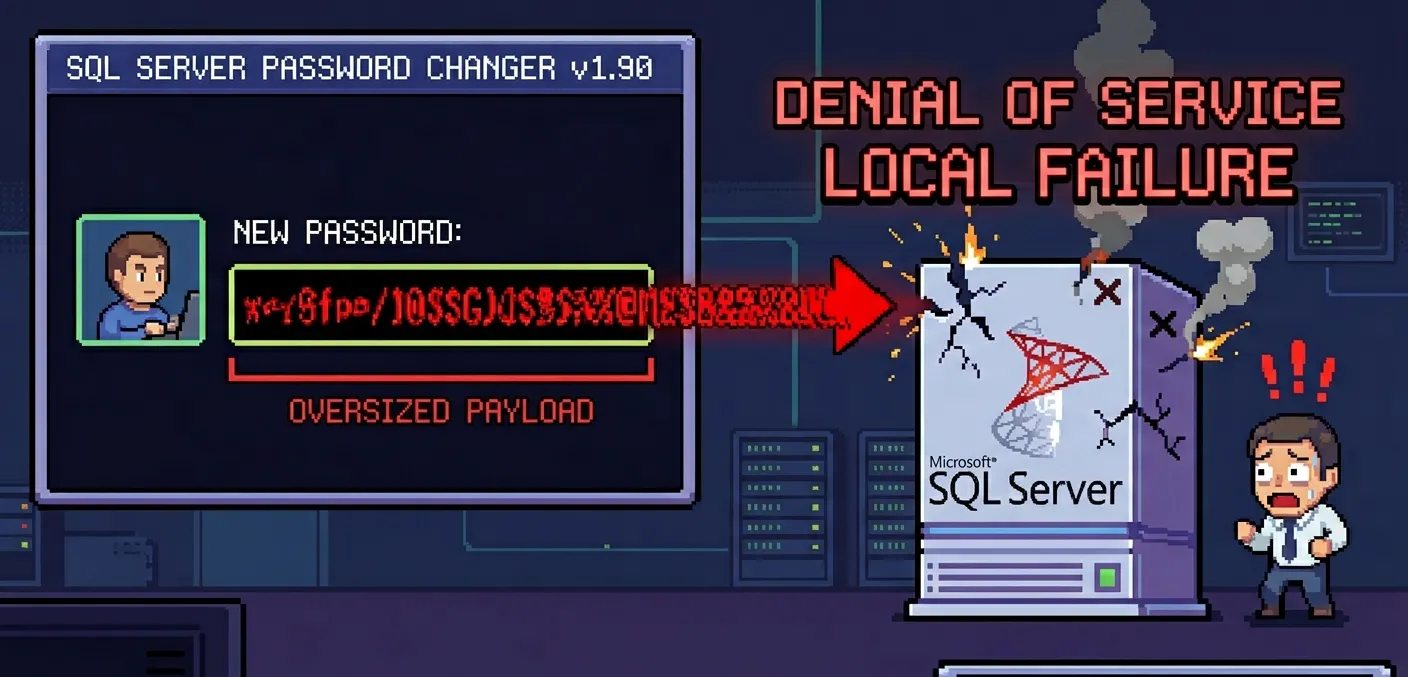
When database administrators reach for third-party utilities to recover or reset SQL Server passwords, they rarely consider whether those tools themselves could become attack vectors. CVE-2019-25475 exposes exactly that blind spot: a classic buffer overflow vulnerability in SQL Server Password Changer 1.90, developed by Top Password Software (top-password.com), that allows an attacker with local access to crash the application by providing an oversized input payload. The vulnerability, classified under CWE-787: Out-of-bounds Write, was first demonstrated through a publicly available exploit on Exploit-DB in August 2019, yet it did not receive its formal NVD entry until March 2026 — a seven-year gap that underscores how legacy desktop utilities can harbor dangerous flaws for extended periods without proper tracking or remediation.
This article provides a thorough technical breakdown of CVE-2019-25475: how the exploit works at the memory level, why the underlying coding pattern is dangerous, what the real-world implications are for enterprise environments, and how developers and administrators can protect themselves from this category of vulnerability. Whether you maintain legacy Windows utilities, manage DBA workstations, or simply want to understand buffer overflow mechanics in a concrete, reproducible context, this analysis will give you actionable depth.
What Is CVE-2019-25475
CVE-2019-25475 is a buffer overflow vulnerability in SQL Server Password Changer version 1.90, a Windows desktop application published by Top Password Software. The tool is designed to help administrators reset or recover SQL Server sa passwords and other database credentials without requiring access to the running SQL Server instance. Users interact with a standard Windows GUI that includes fields for registration information — specifically, the "User Name and Registration Code" dialog.
The vulnerability occurs when an oversized string is supplied to the registration input field. The application allocates a fixed-size buffer to hold the user-supplied data but performs no bounds checking on the input length. When approximately 6,000 bytes of data are pasted into the field, the input overwrites adjacent memory regions on the stack, corrupting stack metadata and the return address. This triggers an access violation, causing the application to crash immediately.
The vulnerability was discovered and reported by security researchers Velayutham Selvaraj and Praveen Thiyagarayam from TwinTech Solutions. Their proof of concept was published on Exploit-DB on August 29, 2019, under EDB-ID 47318. Testing was conducted on Windows 8 x64 and Windows 7 x64 systems.
From a scoring perspective, the CVSS v3.1 base score is 6.2 MEDIUM with a vector string of AV:L/AC:L/PR:N/UI:N/S:U/C:N/I:N/A:H. The CVSS v4.0 score is 6.9 MEDIUM. The attack vector is local, meaning the attacker must have access to the machine where the software is installed. The attack complexity is low — no special conditions or race conditions need to be met. No privileges are required, and no user interaction beyond running the application is necessary. The impact is limited to availability: the application crashes (denial of service), but there is no confirmed data exfiltration or integrity compromise.
Technical insight: The fact that CVSS scores no confidentiality or integrity impact does not mean this vulnerability is benign. A local buffer overflow that overwrites the return address is architecturally identical to those used for arbitrary code execution. The difference between a DoS and a full RCE often comes down to whether the attacker can control the overwritten values precisely enough to redirect execution flow. Modern exploit mitigations like DEP and ASLR make this harder but not impossible, especially on older Windows versions like 7 and 8 where ASLR entropy is limited.
Practical scenario: A junior DBA downloads SQL Server Password Changer to recover a forgotten sa password on a development server. The tool sits on their workstation alongside production management consoles. An attacker with access to that workstation — through a compromised user account, physical access, or lateral movement — can exploit CVE-2019-25475 to crash the tool at a critical moment, potentially disrupting a time-sensitive password recovery operation.
In summary, CVE-2019-25475 is a straightforward but illustrative buffer overflow: a desktop utility that trusts user input implicitly, allocates a fixed buffer, and crashes when that trust is violated.
Understanding CWE-787: Out-of-bounds Write
CWE-787, "Out-of-bounds Write," describes a class of vulnerabilities where software writes data past the boundaries of an allocated memory buffer. This is one of the most prevalent and dangerous weakness types in systems programming, consistently appearing in MITRE's CWE Top 25 Most Dangerous Software Weaknesses. The core problem is deceptively simple: a program allocates N bytes of memory for a buffer but writes more than N bytes into it, overwriting whatever data resides in the adjacent memory locations.
In the context of CVE-2019-25475, the out-of-bounds write occurs on the stack. When the registration dialog function is called, the runtime allocates a local buffer on the stack frame to hold the user's input. The function then copies the input string into this buffer using a function (likely strcpy, lstrcpy, or a similar unbounded copy operation) that has no concept of the destination buffer's size. When the input exceeds the buffer's capacity, the excess bytes spill into adjacent stack memory, overwriting saved registers, frame pointers, and crucially, the return address.
The return address is a pointer stored on the stack that tells the CPU where to resume execution after the current function completes. When this value is corrupted with arbitrary data (in this case, 0x41414141 — the hex representation of "AAAA"), the CPU attempts to jump to an invalid memory address upon function return, triggering an access violation and crashing the process.
Stack-Based vs Heap-Based Overflows
Buffer overflows can target two primary memory regions: the stack and the heap. Each has distinct characteristics and exploitation implications.
Stack-based overflows, like CVE-2019-25475, are the classic variant. The stack follows a Last-In-First-Out (LIFO) discipline, with function call metadata — return addresses, saved base pointers, local variables — arranged in a predictable, contiguous layout. This predictability is a double-edged sword: it makes the stack efficient for function call management but also makes overflow exploitation relatively straightforward. An attacker who can control the data that overwrites the return address can redirect execution to arbitrary code. Stack-based overflows are typically easier to trigger and exploit than heap-based ones because the memory layout is deterministic and the critical control data (return address) is always at a known offset from the buffer.
Heap-based overflows target dynamically allocated memory. The heap's layout is managed by the memory allocator and is far less predictable than the stack. Exploitation requires overwriting heap metadata structures (like free-list pointers) or adjacent heap-allocated objects to achieve control flow hijacking. Heap exploits are generally more complex to develop but can be equally devastating.
Technical insight: In the case of SQL Server Password Changer, the stack-based nature of the overflow is evident from the crash behavior. The application dies with an access violation at address 0x41414141 (or a similar pattern derived from the overflow payload), which is the corrupted return address. If this were a heap overflow, the crash would typically manifest differently — often as a corruption detected during a subsequent malloc or free operation, or as an access violation at an address derived from corrupted heap metadata rather than a clean pattern from the input data.
Practical scenario: Understanding whether an overflow is stack-based or heap-based determines your mitigation strategy. Stack-based overflows can be detected at compile time by enabling stack canaries (GS flag in MSVC). Heap overflows require different defenses, such as heap integrity checking and guard pages. For CVE-2019-25475, simply recompiling the application with the /GS flag in Visual Studio would have prevented exploitation by detecting the stack corruption before the function returned.
Technical Analysis of the Exploit
The exploit for CVE-2019-25475 is remarkably simple, which is itself a telling indicator of the severity of the underlying coding flaw. There is no need for complex ROP chains, heap spraying, or shellcode — the application can be crashed with nothing more than a text file and a clipboard paste operation.
Proof of Concept Breakdown
The proof of concept, published by Velayutham Selvaraj and Praveen Thiyagarayam, uses a minimal Python script to generate the overflow payload:
#!/usr/bin/env python
buffer = "x41" * 6000
try:
f = open("Evil.txt", "w")
print "[+] Creating %s bytes evil payload.." % len(buffer)
f.write(buffer)
f.close()
print "[+] File created!"
except:
print "File cannot be created"The script generates a file named Evil.txt containing 6,000 repetitions of the character "A" (hex 0x41). The exploitation procedure follows these steps:
- Run the Python script to generate
Evil.txtcontaining the 6,000-byte payload. - Open SQL Server Password Changer 1.90 on the target Windows system.
- Navigate to the registration dialog ("User Name and Registration Code" field).
- Open
Evil.txt, select all content, and copy it to the clipboard. - Paste the 6,000-byte string into the registration input field.
- Click the "OK" button to submit the registration data.
- The application immediately crashes with an access violation.
The simplicity of this exploit chain is notable. There is no network component, no privilege escalation, no file system manipulation beyond creating a text file. The entire attack fits in a dozen lines of Python and a manual paste operation. This is characteristic of vulnerabilities in legacy Windows desktop applications that were developed without modern security practices.
The following SVG animation illustrates the buffer overflow mechanism at the memory level, showing how the 6,000-byte payload overwrites critical stack structures:
The animation above demonstrates three phases: first, a normal input fitting safely within the allocated buffer; second, the 6,000-byte overflow payload extending well beyond the buffer boundary, overwriting stack metadata and the saved return address; and third, the resulting access violation when the CPU attempts to execute code at the corrupted address 0x41414141.
Real-World Impact in Enterprise Environments
While a CVSS score of 6.2 and a local attack vector might initially suggest limited risk, the real-world impact of CVE-2019-25475 depends entirely on the operational context in which SQL Server Password Changer is deployed.
Attack Scenario: Shared DBA Workstation
Consider a mid-sized enterprise with a team of three database administrators who share a privileged workstation for SQL Server management tasks. This workstation has SQL Server Management Studio, various third-party DBA tools — including SQL Server Password Changer — and direct network access to production database servers. The workstation runs Windows 7 x64 (still common in enterprise environments with legacy compatibility requirements).
An attacker who gains access to this workstation through any means — phishing a DBA's credentials, exploiting an unpatched browser vulnerability, or leveraging a compromised VPN — now has a local attack surface that includes CVE-2019-25475. The attacker can:
- Disrupt password recovery operations: If a DBA is using SQL Server Password Changer during a critical incident (e.g., a production database with a forgotten sa password), crashing the tool delays recovery and extends downtime. In a scenario where every minute of database unavailability costs thousands of dollars, this is a meaningful impact.
- Use the crash as a pivot for investigation: The crash dump generated by the application may contain sensitive information — fragments of passwords, connection strings, or database metadata that were in memory at the time of the crash. Windows Error Reporting (WER) captures these dumps automatically, and they may persist on disk in accessible locations.
- Explore further exploitation: The buffer overflow that currently causes a crash could potentially be weaponized for code execution. The PoC uses a uniform 0x41 pattern, but a skilled attacker could craft a payload that places shellcode in the buffer and overwrites the return address with a pointer to that shellcode. On Windows 7 without full ASLR coverage, this is a realistic escalation path.
Performance and scalability consideration: In enterprise environments, the presence of vulnerable tools like SQL Server Password Changer creates a lateral attack surface that scales with the number of workstations. If the tool is deployed across 50 DBA workstations (as part of a standard toolkit image), each workstation becomes a potential point of exploitation. The unpatched nature of this vulnerability — no fix has been confirmed from the vendor — means that the attack surface persists indefinitely until the tool is removed from all systems.
Common Developer Mistakes That Lead to Buffer Overflows
CVE-2019-25475 is not an isolated incident. It exemplifies a category of coding errors that have persisted for decades despite being well-understood. Here are the five most common developer mistakes that lead to buffer overflow vulnerabilities:
- Using unbounded string copy functions. Functions like
strcpy,strcat,sprintf, and their Windows equivalents (lstrcpy,wsprintf) copy data until they encounter a null terminator, with no regard for the destination buffer's size. SQL Server Password Changer almost certainly uses one of these functions to copy registration input into a fixed-size stack buffer. The fix is to use bounded alternatives:strncpy,strncat,snprintf, or preferably the safer_svariants (strcpy_s,strcat_s) that take an explicit buffer size parameter and trigger a runtime error on overflow. - Trusting GUI input without length validation. Developers often assume that because a text field appears small on screen, users will only enter short strings. This is a fundamentally flawed assumption. Windows edit controls have no inherent length limit unless one is explicitly set via the
EM_SETLIMITTEXTmessage. SQL Server Password Changer could have prevented the overflow at the UI level by limiting the input field to a reasonable maximum length — perhaps 256 characters for a registration code. This is defense in depth: it does not fix the underlying buffer issue, but it prevents the most obvious exploitation path. - Allocating fixed-size stack buffers for variable-length input. Declaring a local array like
char buffer[256]and then copying user input into it without checking the input length is the textbook recipe for a stack-based overflow. The alternative is to either dynamically allocate memory based on the actual input length (usingmallocornew) or to use safe string containers likestd::stringin C++ that manage their own memory. - Ignoring compiler security warnings and flags. Modern compilers offer multiple defenses against buffer overflows: stack canaries (/GS in MSVC), buffer security checks, and Control Flow Guard (CFG). Many legacy applications were compiled without these protections because they were either unavailable at the time or because developers disabled them for performance reasons. SQL Server Password Changer 1.90, likely compiled with an older version of Visual Studio, probably lacks these mitigations entirely.
- Skipping fuzz testing during development. Fuzz testing — automatically generating malformed, oversized, or randomized inputs and feeding them to the application — would have caught this vulnerability instantly. A fuzzer would have generated a 6,000-character string for the registration field within seconds of starting a test run. The absence of any fuzzing in the development process is a clear indicator of insufficient quality assurance practices.
Mitigation and Prevention Strategies
Addressing CVE-2019-25475 requires both immediate tactical responses and longer-term strategic changes. Since no patch has been confirmed from Top Password Software, the burden of mitigation falls entirely on the users and organizations deploying this tool.
Input Validation Best Practices
- Set explicit input length limits at the UI layer. For Windows GUI applications, use the
EM_SETLIMITTEXTmessage to restrict the maximum number of characters a text field will accept. For registration codes, a limit of 128-256 characters is more than sufficient. - Validate input length before any copy operation. Before copying user input into a buffer, check the input's length against the buffer's capacity. If the input exceeds the limit, reject it with an error message rather than attempting to copy it.
- Use bounded string functions exclusively. Replace all instances of
strcpy,strcat, andsprintfwith their bounded counterparts (strcpy_s,strcat_s,sprintf_s). These functions take a buffer size parameter and fail safely when the input would exceed the buffer. - Sanitize input at multiple layers. Do not rely on a single validation point. Validate at the UI layer, validate again in the business logic layer, and validate once more before any memory operation. Defense in depth ensures that a bypass at one layer does not result in exploitation.
- Implement input canonicalization. Before validation, normalize the input to a standard form. This prevents encoding tricks (such as Unicode normalization attacks) from bypassing length checks that only count raw bytes.
Memory-Safe Development Approaches
- Migrate to memory-safe languages where feasible. For new development, consider Rust, Go, or managed languages (C#, Java) that eliminate entire classes of memory safety vulnerabilities. For existing C/C++ codebases, identify the highest-risk components (user input handling, file parsing) and prioritize rewriting those modules in a memory-safe language.
- Enable all available compiler security features. For MSVC: enable /GS (stack buffer overrun detection), /DYNAMICBASE (ASLR), /NXCOMPAT (DEP), and /guard:cf (Control Flow Guard). For GCC/Clang: enable -fstack-protector-all, -D_FORTIFY_SOURCE=2, and -pie. These do not fix the underlying vulnerability but significantly raise the bar for exploitation.
- Adopt AddressSanitizer (ASan) during development. ASan instruments memory access at compile time and detects out-of-bounds reads and writes, use-after-free, and other memory errors at runtime with minimal performance overhead. Running the test suite with ASan enabled would have caught CVE-2019-25475 immediately.
- Implement automated fuzz testing in CI/CD pipelines. Tools like AFL, libFuzzer, or WinAFL can automatically discover buffer overflows by generating millions of mutated inputs and monitoring for crashes. Integrate fuzzing into your continuous integration pipeline so that every code change is tested against malformed inputs.
- Remove or replace vulnerable tools. For CVE-2019-25475 specifically, the most effective mitigation is to stop using SQL Server Password Changer 1.90 entirely. Evaluate alternative password recovery tools that have been developed with modern security practices, or use Microsoft's built-in password reset procedures which do not rely on third-party software.
Comparison with Similar Buffer Overflow CVEs
CVE-2019-25475 is not unique in the landscape of buffer overflow vulnerabilities affecting desktop utilities. The following table compares it with similar CVEs that share the same fundamental weakness pattern — insufficient input validation leading to out-of-bounds memory writes in user-facing applications:
| CVE | Application | CWE | CVSS | Impact | Vector |
|---|---|---|---|---|---|
| CVE-2019-25475 | SQL Server Password Changer 1.90 | CWE-787 | 6.2 Medium | DoS (application crash) | Local — oversized registration input |
| CVE-2019-25478 | GetGo Download Manager | CWE-787 | 6.5 Medium | DoS (application crash) | Local — crafted input in URL field |
| CVE-2019-25471 | FileZilla 3.33.0 | CWE-787 | 5.5 Medium | DoS (client crash) | Local — oversized hostname input |
| CVE-2018-1922 | IBM Db2 | CWE-119 | 8.4 High | Code execution / DoS | Local — crafted Db2 command |
Several patterns emerge from this comparison. First, all four vulnerabilities share the same root cause: unbounded copy of user input into fixed-size buffers. Second, three of the four share a local attack vector, while CVE-2019-25478 demonstrates that the same overflow pattern can be exploited remotely over the network. Third, the impact ranges from denial of service (CVE-2019-25475, CVE-2019-25478) to full code execution (CVE-2019-25612, CVE-2018-1922), illustrating how the same fundamental flaw can have varying severity depending on the specific memory layout and available exploit mitigations. The IBM Db2 vulnerability is particularly notable because it demonstrates that even enterprise-grade database software from major vendors is not immune to buffer overflow vulnerabilities, and its higher CVSS score reflects the confirmed potential for arbitrary code execution.
Frequently Asked Questions
Is CVE-2019-25475 exploitable for remote code execution?
The published proof of concept only demonstrates denial of service through an application crash. However, the underlying mechanism — overwriting the saved return address on the stack — is the same technique used in code execution exploits. Whether RCE is achievable depends on factors such as the presence of DEP, ASLR, stack canaries, and the specific memory layout of the application. On older systems like Windows 7 without full ASLR, escalation from crash to code execution is theoretically possible with a more sophisticated payload. The vulnerability should be treated as potentially more dangerous than the published PoC suggests.
Has Top Password Software released a patch for this vulnerability?
As of the NVD publication date (March 11, 2026), no patch has been confirmed from Top Password Software. The vendor's website (top-password.com) lists SQL Server Password Changer but does not reference CVE-2019-25475 or provide a patched version. Organizations using this tool should consider it permanently vulnerable and plan for replacement rather than waiting for a fix.
What operating systems are affected?
The exploit was tested and confirmed on Windows 8 x64 and Windows 7 x64. However, since the vulnerability resides in the application's code rather than in an OS-specific API, it is likely exploitable on any Windows version that can run the software, including Windows 10 and Windows 11. Newer operating systems may offer better exploit mitigations (stronger ASLR, CFG) that could prevent escalation from crash to code execution, but the denial of service condition will still occur regardless of the OS version.
Can antivirus or endpoint protection detect this exploit?
Traditional antivirus solutions are unlikely to detect or prevent this exploit. The payload is a simple string of "A" characters — there is no malicious shellcode, no known signature, and no network-based indicator. Endpoint Detection and Response (EDR) solutions with behavioral analysis capabilities might detect the anomalous crash pattern (repeated access violations in the same application), but they would only provide post-incident alerting rather than prevention. The most effective defense is removing the vulnerable software entirely.
Should we remove SQL Server Password Changer from all systems?
Yes. Given the absence of a vendor patch and the well-documented exploitation path, the recommended action is to remove SQL Server Password Changer 1.90 from all systems. If you need SQL Server password recovery capabilities, evaluate alternative tools that have active security maintenance and have been developed with modern memory-safe practices. Microsoft also provides built-in procedures for resetting SQL Server passwords through single-user mode that do not require third-party software.
CVE-2019-25475 serves as a concrete reminder that every tool installed on a privileged workstation expands the attack surface. The buffer overflow in SQL Server Password Changer 1.90 is technically simple, publicly documented, and permanently unpatched — a combination that demands immediate action. Audit your DBA workstations, remove unnecessary third-party utilities, and ensure that any tools you do retain have been built with the security practices this article outlines. The cost of ignoring legacy vulnerabilities compounds over time; address them proactively before an attacker makes the decision for you.
References
- CVE-2019-25475: Buffer Overflow in SQL Server Password Changer — National Vulnerability Database (NVD)
- SQL Server Password Changer 1.90 - Denial of Service (EDB-ID 47318) — Exploit-DB
- SQL Server Password Changer 1.90 Denial of Service Buffer Overflow — VulnCheck
- CWE-787: Out-of-bounds Write — MITRE
- CVE-2019-25478: Buffer Overflow in GetGo Download Manager — NVD
- CVE-2019-25612: Buffer Overflow in Admin Express — NVD
- CVE-2018-1922: Buffer Overflow in IBM Db2 — NVD
- Security Bulletin: Multiple Buffer Overflow Vulnerabilities in IBM Db2 — IBM
Share this post
Subscribe
Get the latest posts delivered right to your inbox.



Leave a comment