Cybersecurity
CVE-2026-29784: Ghost CMS CSRF Flaw in Session Verification
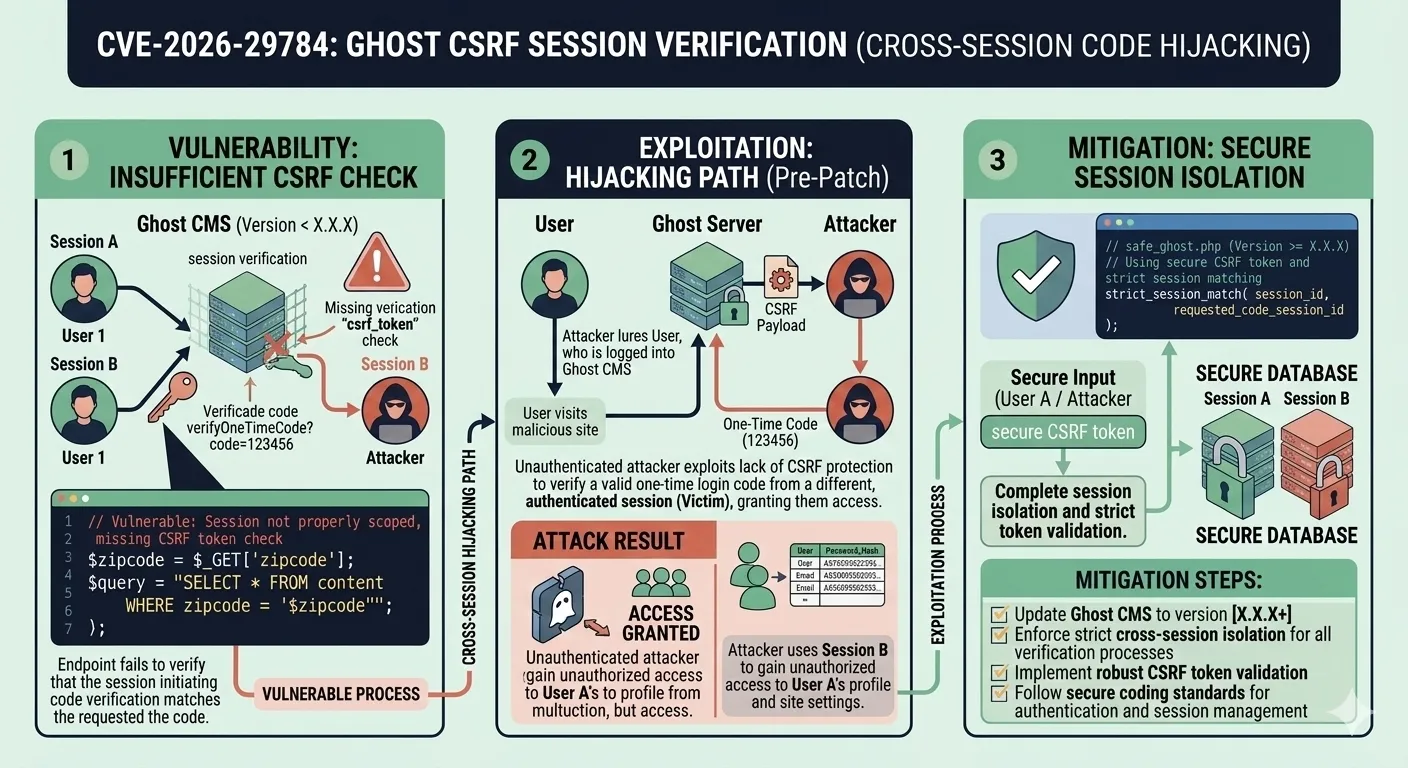
The disclosure of CVE-2026-29784 brings into sharp focus a vulnerability class that many Node.js developers underestimate: Cross-Site Request Forgery targeting authentication endpoints. Ghost, widely regarded as one of the most polished headless CMS platforms for professional publishing, carried an incomplete CSRF protection in its /session/verify endpoint from version 5.101.6 through 6.19.2. The flaw allowed One-Time Codes (OTCs) issued during login to be consumed by sessions different from the one that originally requested them. In practice, this meant a well-crafted phishing campaign could grant an attacker full administrative access to a Ghost installation without ever needing to crack a password. For engineering teams operating Ghost at scale, the implications extend beyond a simple patch. This vulnerability reveals fundamental lessons about session binding, CSRF token lifecycle management, and the architectural decisions that separate resilient authentication systems from fragile ones. In this article, we dissect the mechanics of CVE-2026-29784, explore its real-world exploitation potential, and outline the defensive strategies every team building session-based authentication should adopt.
What is CVE-2026-29784?
CVE-2026-29784 is a security vulnerability in Ghost CMS that stems from incomplete CSRF protections on the /session/verify endpoint. Ghost uses a passwordless One-Time Code (OTC) system for administrator login. When a user initiates a login, Ghost generates a short-lived code and sends it to the registered email address. The user then submits this code to /session/verify to complete authentication.
The core issue is that the endpoint did not fully validate whether the OTC submission originated from the same session that requested the code. A valid CSRF token was required, but the session-binding check was incomplete. This gap meant that if an attacker obtained a legitimate OTC through phishing or social engineering, they could submit it from their own browser session and gain authenticated access to the Ghost admin panel.
Affected Versions and Severity
The vulnerability affects all Ghost installations running versions 5.101.6 through 6.19.2. The Ghost team resolved the issue in version 6.19.3 by enforcing strict session binding during OTC verification. While the CVSS score reflects a medium severity given the social engineering prerequisite, the potential impact is critical: complete administrative takeover of a publishing platform, including the ability to modify content, inject scripts, access subscriber data, and alter site configuration.
Understanding CSRF in Modern Web Applications
Cross-Site Request Forgery remains one of the most persistent web security challenges despite decades of awareness. A CSRF attack exploits the trust that a web application places in the user's browser. When a user is authenticated, their browser automatically attaches session cookies to every request sent to that domain. An attacker who tricks the user into visiting a malicious page can leverage those cookies to submit forged requests that the server treats as legitimate.
What makes CVE-2026-29784 particularly instructive is that Ghost did implement CSRF protections. The vulnerability was not a complete absence of defense but rather an incomplete implementation. This is a common pattern in real-world security incidents: partial mitigations that appear secure during development but leave exploitable gaps when attackers approach them from unexpected angles.
Why Session Binding is Non-Negotiable
Session binding means ensuring that a security token or authentication artifact is cryptographically tied to the specific session that created it. Without session binding, tokens become transferable. In Ghost's case, the OTC was validated as authentic but not verified as belonging to the requesting session. Think of it like a boarding pass that verifies your identity but does not check which gate you departed from. The token is real, but the context is wrong.
A developer commonly makes the mistake of validating the token's existence and expiry without confirming its session affinity. This is especially dangerous in passwordless flows where the OTC effectively replaces the password as the sole authentication factor.
Ghost CMS Authentication Architecture
Ghost's authentication system is designed around simplicity and security for content creators. Rather than relying on traditional username-password combinations, Ghost adopted a passwordless approach using email-delivered One-Time Codes. This design eliminates credential stuffing attacks and removes the burden of password management from users. However, it shifts the security perimeter to the OTC validation flow itself.
The One-Time Code Login Flow
Understanding the standard OTC flow is essential to grasp why CVE-2026-29784 is exploitable. The process follows these steps:
- The administrator navigates to the Ghost admin panel and enters their email address.
- Ghost generates a cryptographically random OTC, stores it server-side with the associated email and session identifier, and sends it via email.
- The administrator retrieves the code from their inbox and submits it through the
/session/verifyendpoint. - Ghost validates the code, checks expiry, and (in patched versions) verifies session binding before granting an authenticated session.
The following animated diagram illustrates how CVE-2026-29784 disrupts this flow, allowing an attacker to intercept the OTC and use it in a separate session:
The Attack Vector: Cross-Session OTC Exploitation
The exploitation of CVE-2026-29784 requires a combination of social engineering and the technical flaw in session binding. The attack unfolds when a legitimate Ghost administrator initiates a login and receives an OTC via email. The attacker, through a phishing page or direct social engineering, persuades the administrator to reveal the OTC. Because the /session/verify endpoint did not enforce that the OTC must be submitted from the same session that requested it, the attacker can submit the stolen OTC from their own browser and receive a fully authenticated administrator session.
This is fundamentally different from a simple credential theft scenario. In a password-based system, stealing the password alone is sufficient. In Ghost's OTC system, the OTC was meant to be a session-bound artifact, adding a layer of protection. CVE-2026-29784 neutralized that layer, reducing the OTC to a transferable secret no different from a static password.
Phishing Scenario in Practice
Consider a real-world scenario where a mid-size digital publication runs Ghost for their editorial workflow. An attacker crafts a convincing email impersonating Ghost's system notifications, asking the administrator to verify a suspicious login attempt. The email links to a phishing page that mimics Ghost's login interface and prompts the victim to enter their OTC. Once captured, the attacker submits the code to the real Ghost instance:
<!-- Attacker's phishing page: auto-submits stolen OTC -->
<form action="https://target-ghost.com/ghost/api/admin/session/verify" method="POST">
<input type="hidden" name="token" value="STOLEN_OTC_VALUE" />
<input type="hidden" name="email" value="admin@target-ghost.com" />
</form>
<script>document.forms[0].submit();</script>The server validates the OTC, finds it unexpired, and because session binding was incomplete, grants the attacker an authenticated admin session. The attacker now controls the publication's entire content pipeline.
Impact on Production Ghost Deployments
The consequences of a successful CVE-2026-29784 exploitation extend far beyond unauthorized access. Ghost administrators have full control over published content, theme configuration, integrations, and subscriber data. An attacker with admin access can inject malicious JavaScript into published articles, redirect traffic, exfiltrate subscriber email lists, or deface the publication entirely. For organizations using Ghost as a revenue-generating platform, the business impact includes reputational damage, legal liability for data exposure, and potential loss of advertising revenue.
Scalability Concerns in Multi-Site Environments
Organizations running multiple Ghost instances behind a shared reverse proxy face amplified risk. If administrators reuse email addresses across instances or if the reverse proxy's session management interacts with Ghost's session cookies, a single successful phishing attack could cascade across multiple publications. In multi-tenant Ghost Pro deployments, the isolation between tenant sessions becomes a critical architectural boundary that must be validated independently of Ghost's own session management.
Common CSRF Protection Mistakes Developers Make
CVE-2026-29784 is a textbook example of a partial security implementation that creates a false sense of safety. The following are the most frequent mistakes developers make when implementing CSRF defenses, each of which can lead to vulnerabilities similar to this one:
- Validating the token but not the session: Checking that a CSRF token exists and is valid without confirming it belongs to the current session. This is exactly the gap CVE-2026-29784 exploited.
- Relying solely on SameSite cookies: While
SameSite=StrictorSameSite=Laxprevents many CSRF vectors, they do not protect against all scenarios, particularly when the attacker controls a subdomain or when the application uses GET requests for state-changing operations. - Skipping Origin and Referer header validation: These headers provide a secondary verification layer. Many frameworks offer middleware to check them, but developers often disable or misconfigure these checks during development and forget to re-enable them.
- Using predictable or reusable tokens: CSRF tokens must be cryptographically random and single-use for sensitive operations. Tokens that persist across multiple requests expand the attack window.
- Ignoring CSRF on API endpoints: Teams building JSON APIs sometimes assume that the
Content-Type: application/jsonrequirement acts as implicit CSRF protection. This is incorrect because certain browser features and Flash-based techniques can forge JSON requests with cookies attached.
CSRF Protection Comparison Across CMS Platforms
Understanding how different platforms approach CSRF protection provides context for evaluating Ghost's vulnerability. The following table compares CSRF defense mechanisms across popular CMS solutions:
| CMS Platform | CSRF Token Type | Session Binding | SameSite Cookies | Additional Protections |
|---|---|---|---|---|
| Ghost (pre-6.19.3) | Synchronizer token | Incomplete | Lax | Origin header check |
| Ghost (6.19.3+) | Synchronizer token | Full | Strict | Origin + session binding |
| WordPress | Nonce (time-limited) | User-bound | Lax | Nonce per action |
| Strapi | JWT-based | Token-inherent | None (API-based) | CORS policies |
| Contentful | API key + OAuth | Token-inherent | N/A (SaaS API) | Rate limiting, IP allowlists |
Notice that SaaS-based headless CMS platforms like Contentful avoid browser-based CSRF entirely by relying on API keys and OAuth tokens that are never automatically attached by the browser. Ghost, by operating as a self-hosted platform with a browser-based admin panel, must address CSRF at the application layer, which is inherently more complex.
Patching and Hardening Your Ghost Installation
The immediate fix for CVE-2026-29784 is upgrading to Ghost 6.19.3 or later. The patched version enforces strict session binding on the /session/verify endpoint, ensuring that an OTC can only be consumed by the session that originally requested it.
Verifying Your Ghost Version
Before upgrading, verify your current Ghost version using the CLI:
ghost version
# Or check via the API:
curl -s https://your-ghost-instance.com/ghost/api/admin/site/ | jq '.site.version'If the reported version falls between 5.101.6 and 6.19.2, your instance is vulnerable and requires immediate patching. Upgrade using the standard Ghost CLI procedure:
ghost updateAdditional Security Hardening
Beyond applying the patch, consider implementing the following measures to strengthen your Ghost deployment against similar vulnerabilities:
- Enforce IP-based access controls on the
/ghost/admin path using your reverse proxy (Nginx, Caddy, or a CDN like Cloudflare). - Enable two-factor authentication if available through Ghost extensions or reverse proxy-level authentication.
- Configure Content-Security-Policy headers to prevent inline script execution, which limits the damage from injected payloads even if admin access is compromised.
- Monitor authentication logs for OTC requests originating from unexpected IP addresses or geolocations.
- Set strict SameSite cookie attributes at the reverse proxy level if Ghost's built-in settings do not expose this configuration.
- Implement rate limiting on the
/session/verifyendpoint to throttle brute-force OTC attempts.
Frequently Asked Questions
What exactly does CVE-2026-29784 allow an attacker to do?
CVE-2026-29784 allows an attacker to use a stolen One-Time Code in a browser session different from the one that originally requested it. If the attacker obtains a valid OTC through phishing, they can submit it from their own session and gain full administrative access to the Ghost CMS installation without needing the administrator's password or direct access to their browser.
Is my Ghost site vulnerable if I use a reverse proxy?
A reverse proxy does not mitigate CVE-2026-29784 by itself. The vulnerability exists at the application layer within Ghost's session verification logic. However, a reverse proxy can provide defense-in-depth by restricting access to the /ghost/ admin path by IP address, which reduces the attack surface regardless of the application-layer vulnerability.
Does upgrading to Ghost 6.19.3 require database migration?
The patch in Ghost 6.19.3 primarily modifies the session verification logic and does not introduce breaking schema changes. Standard upgrade procedures using ghost update apply. As always, perform a full backup before upgrading production instances.
Can this vulnerability be exploited without user interaction?
No. CVE-2026-29784 requires social engineering to obtain the OTC from a legitimate administrator. The attacker cannot generate or guess a valid OTC remotely. The vulnerability only becomes exploitable after the attacker acquires a valid code, which requires tricking the victim into revealing it through phishing or similar techniques.
Conclusion
CVE-2026-29784 serves as a reminder that authentication security is only as strong as its weakest binding point. Ghost's OTC system was designed to eliminate password-related risks, but the incomplete CSRF protection on /session/verify reintroduced a transferability flaw that undermined the entire passwordless model. The fix is straightforward: upgrade to Ghost 6.19.3. The broader lesson is not. Every authentication flow that issues session-bound tokens must enforce that binding rigorously at every validation checkpoint. If you operate Ghost in production, verify your version today, apply the patch, and audit your reverse proxy configuration for defense-in-depth measures that protect against the next vulnerability before it is disclosed.
Share this post
Subscribe
Get the latest posts delivered right to your inbox.



Leave a comment